Resecurity is proud to contribute to disrupting of Tycoon 2FA, a cybercriminal platform that generated more than 30 million bogus emails in a single month. The joint effort, led by Microsoft, Europol, and other industry partners, aimed to target its infrastructure responsible for tens of millions of fraudulent emails reaching over 500,000 organizations each month worldwide.

By mid‑2025, Tycoon 2FA accounted for approximately 62 percent of all phishing attempts Microsoft blocked, including more than 30 million emails in a single month. That placed Tycoon 2FA among the largest phishing operations globally. Despite extensive defenses, the service is linked to an estimated 96,000 distinct phishing victims worldwide since 2023, including more than 55,000 Microsoft customers.
Taking this infrastructure offline cuts off a major pipeline for account takeovers and helps protect people and organizations from follow‑on attacks such as data theft, ransomware, business email compromise, and financial fraud.
Resecurity acquired access to Tycoon 2FA, widely used by thousands of cybercriminals to impersonate real users and gain unauthorized access to email and online service accounts, including Microsoft 365, Outlook, and Gmail.
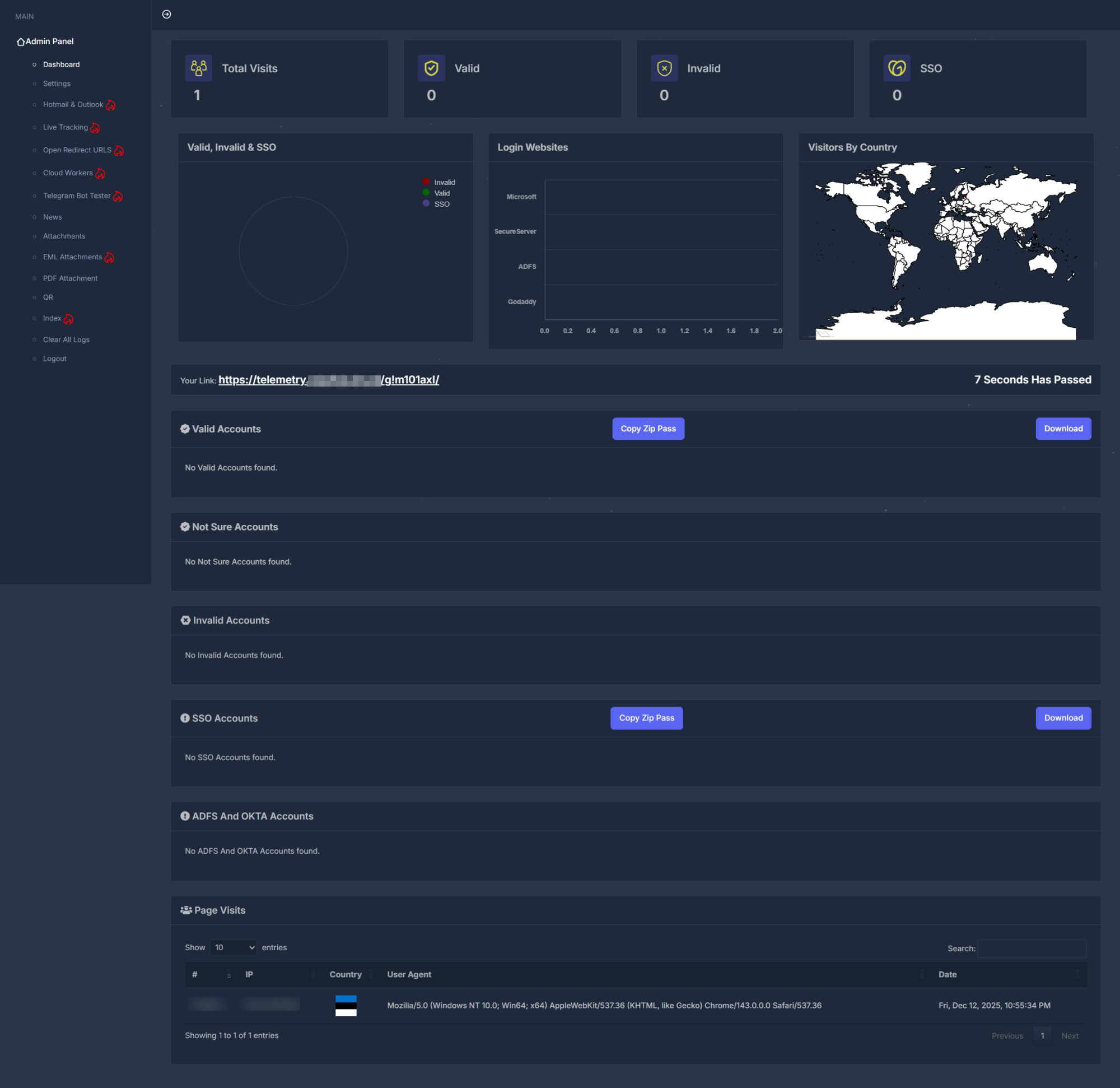
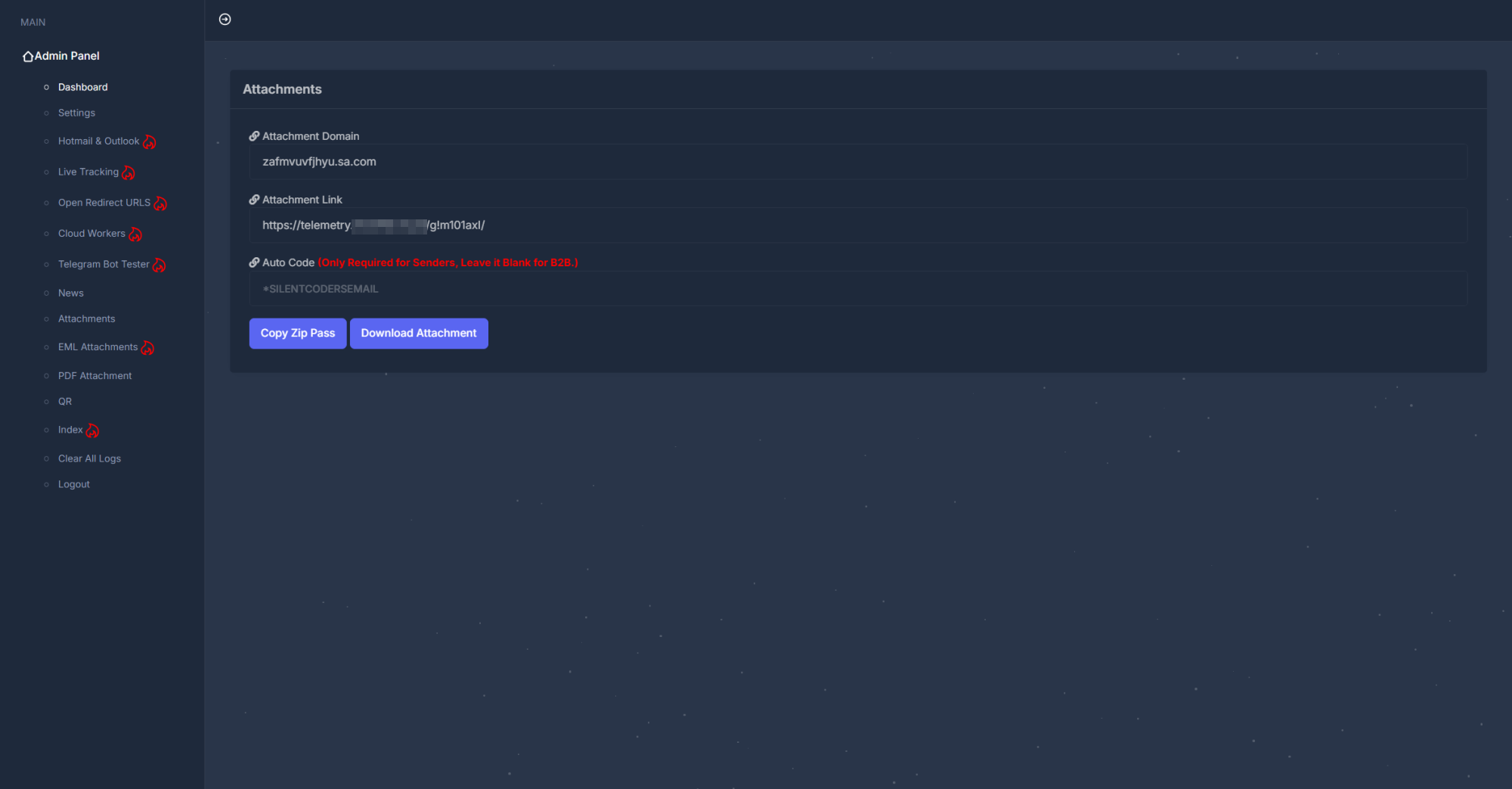
The kit provides an interactive GUI panel and API that enable cybercriminals to automate and scale their operations.
The GUI panel allows users to navigate compromised accounts, with dedicated modules specifically allocated for Hotmail and Outlook.

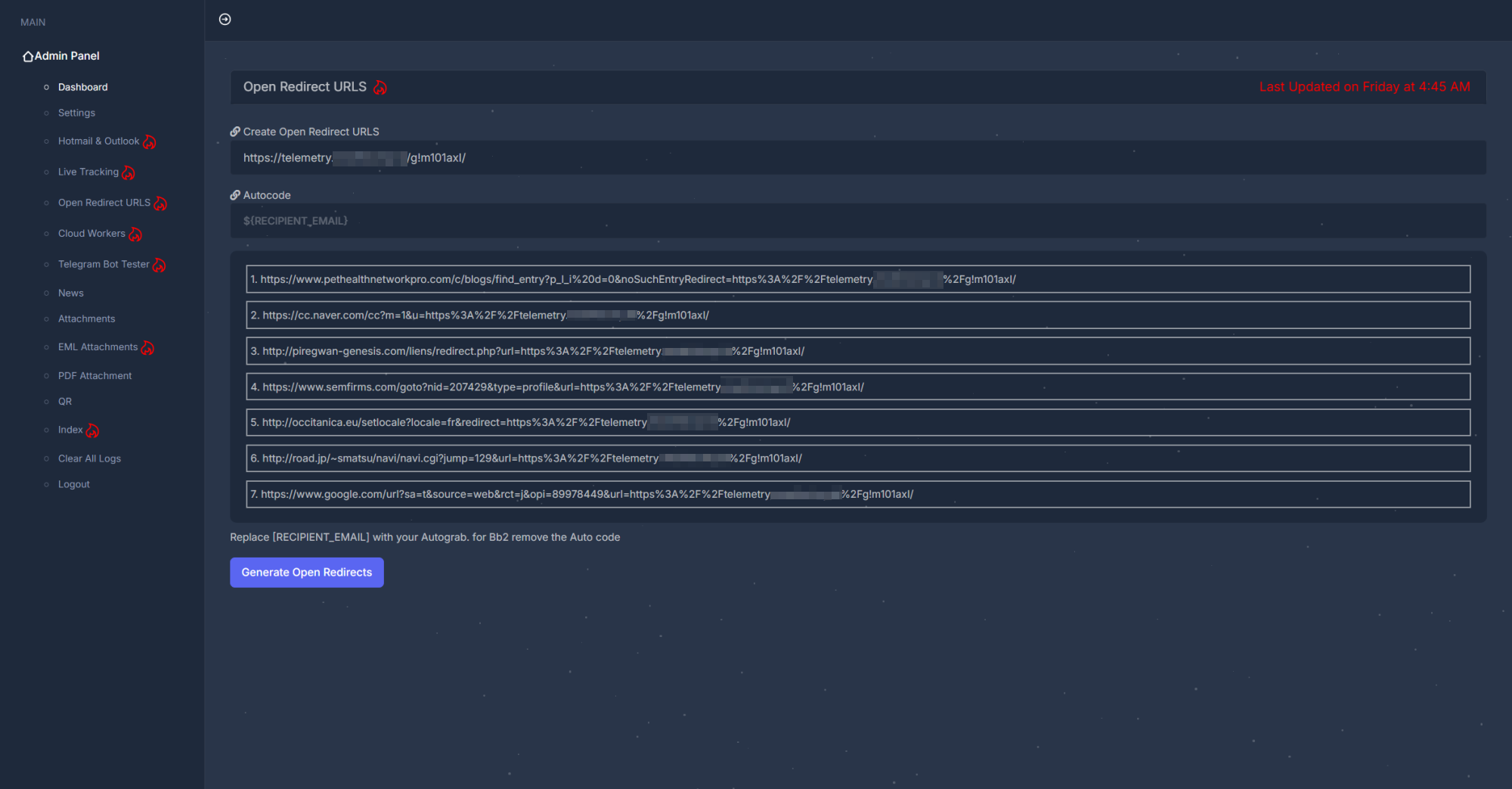
As one of its evasion mechanisms, Tycoon 2FA leverages URL rotation by abusing open redirect vulnerabilities on third-party websites.
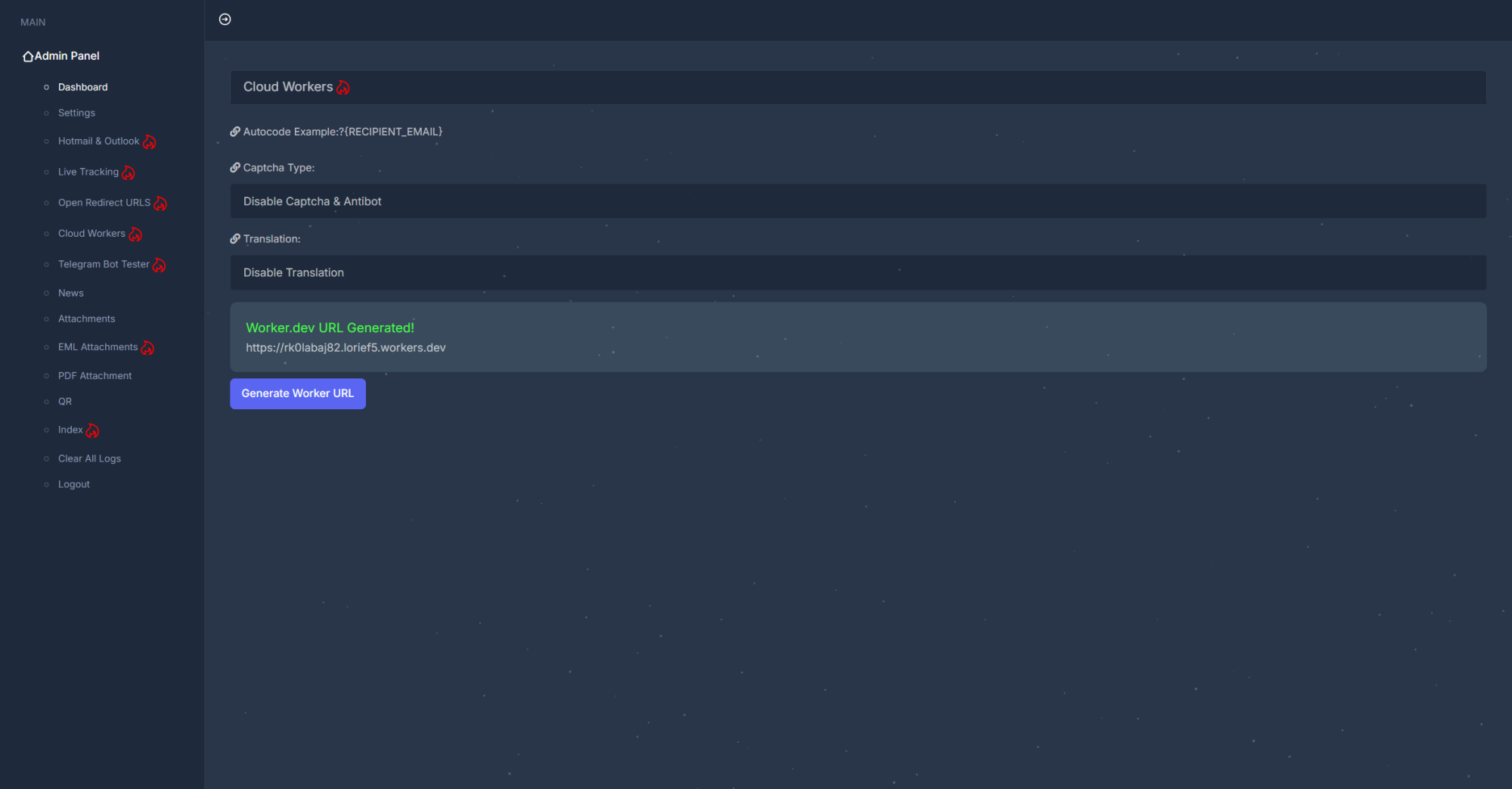
Another mechanism that enables the protection of malicious instances generated by Tycoon 2FA is the misuse of Cloudflare (Workers).
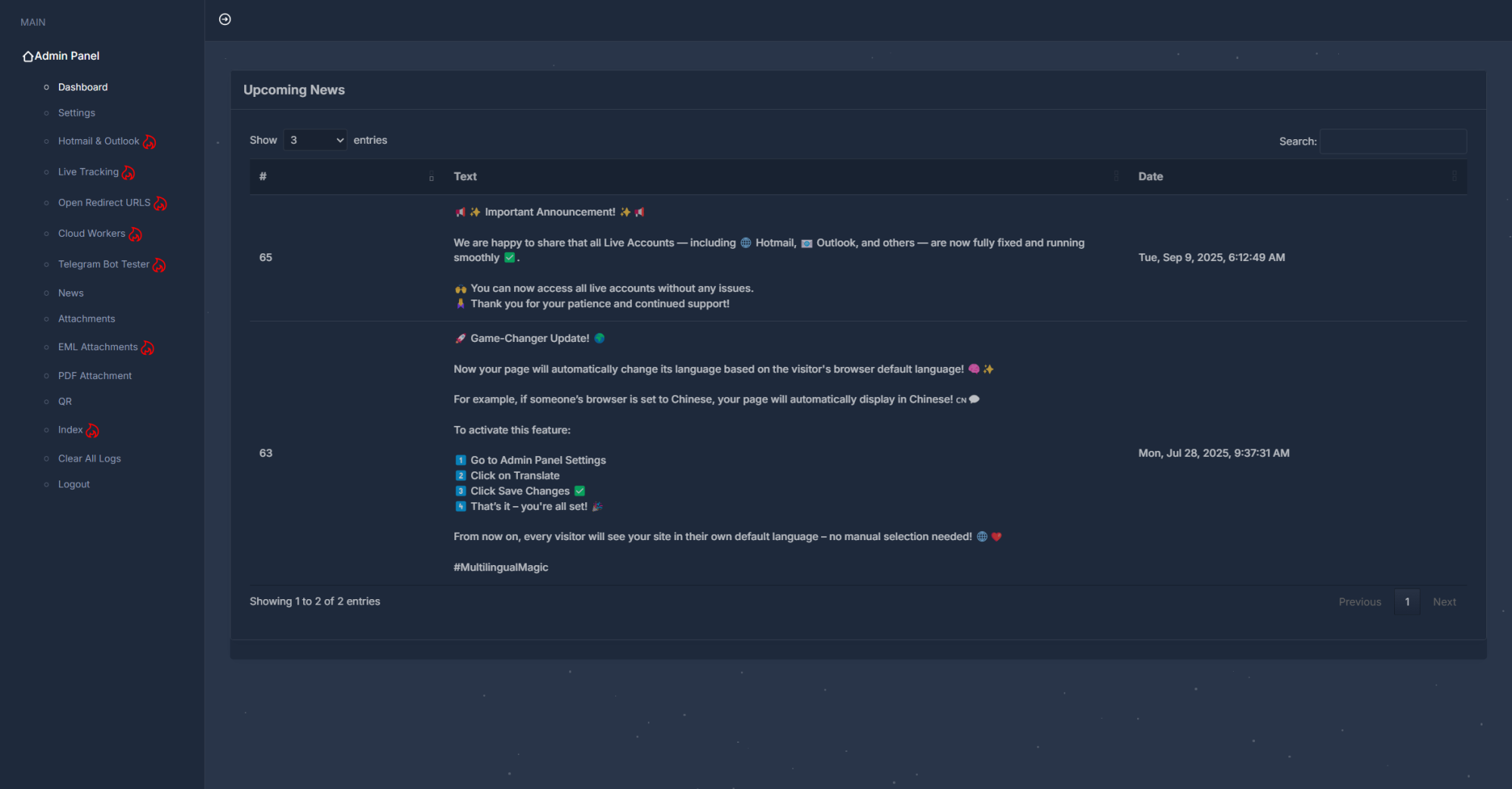
The author of Tycoon 2FA is actively updating the tool with regular kit updates.
What makes Tycoon 2FA so special is that the kit effectively combines multiple methods to deliver phishing at scale—from PDF attachments to QR codes.
Tycoon 2FA allows users to generate malicious emails by impersonating popular brands. Resecurity has identified several notable threat actors using the kit across scenarios—from traditional phishing to more advanced tactics that combine wire fraud and business email compromise (BEC).
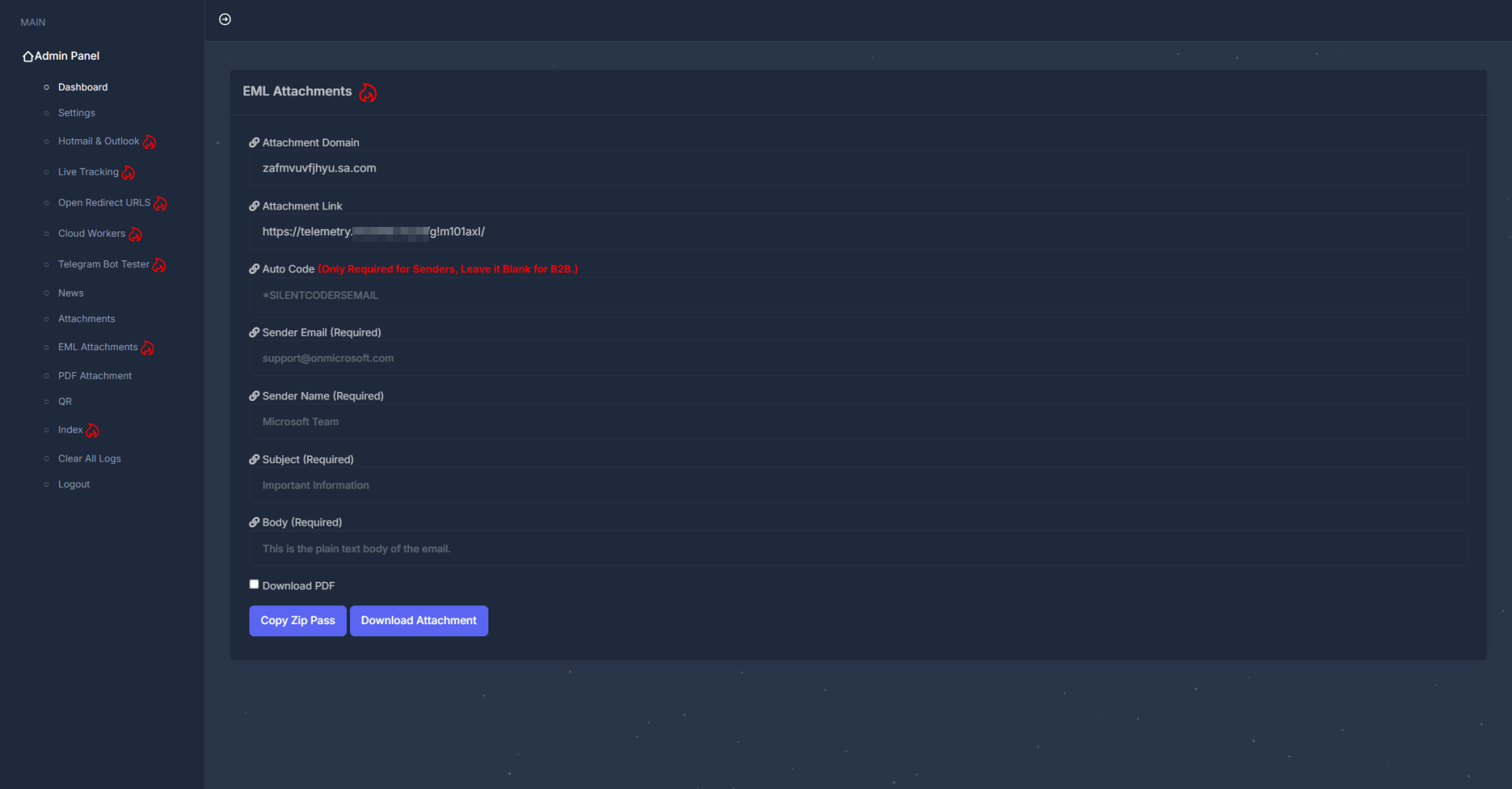
Cybercriminals can generate malicious PDF documents that appear as invoices, banking statements, presentations, and other common documents (e.g., for e-signing) to target consumers worldwide.

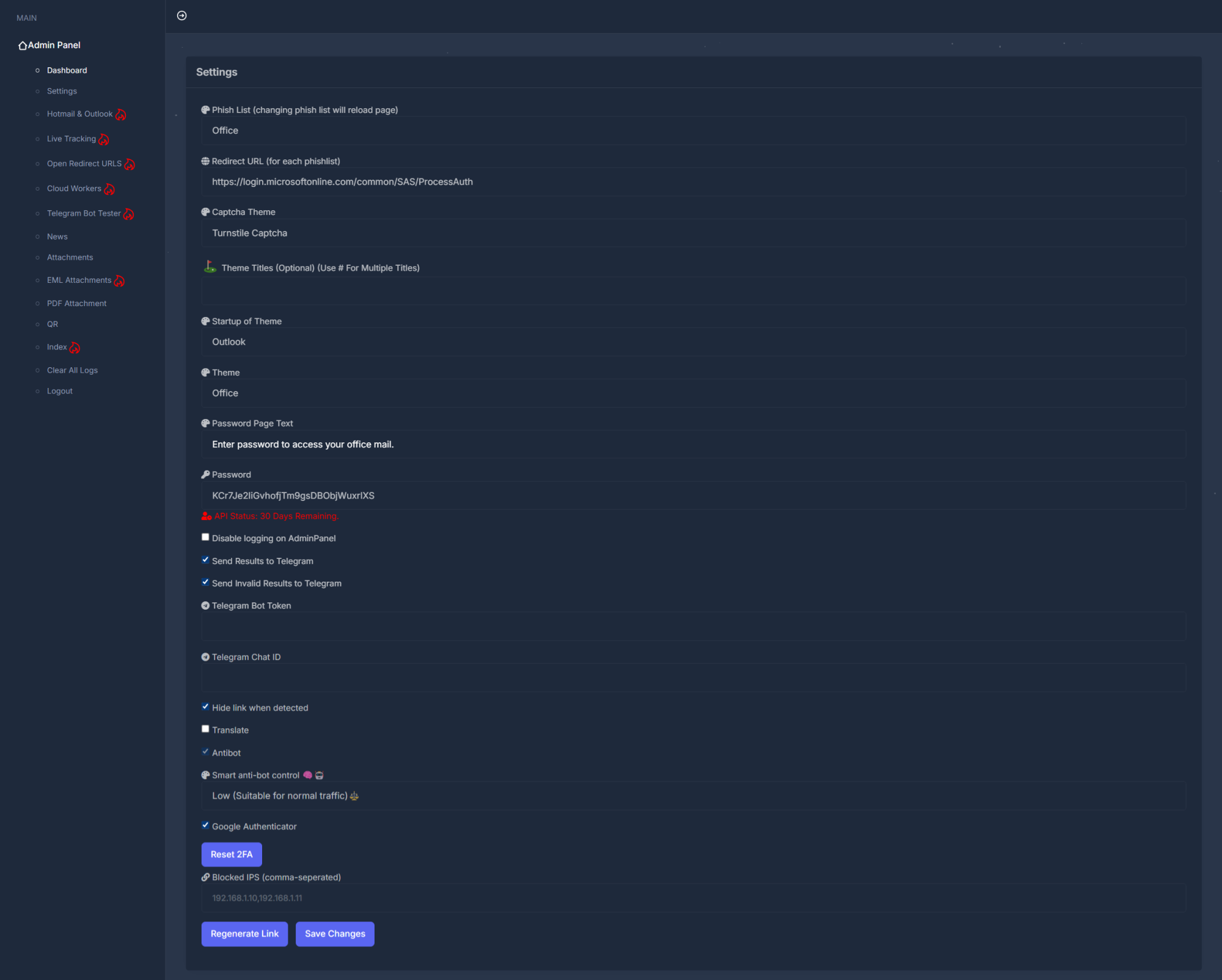
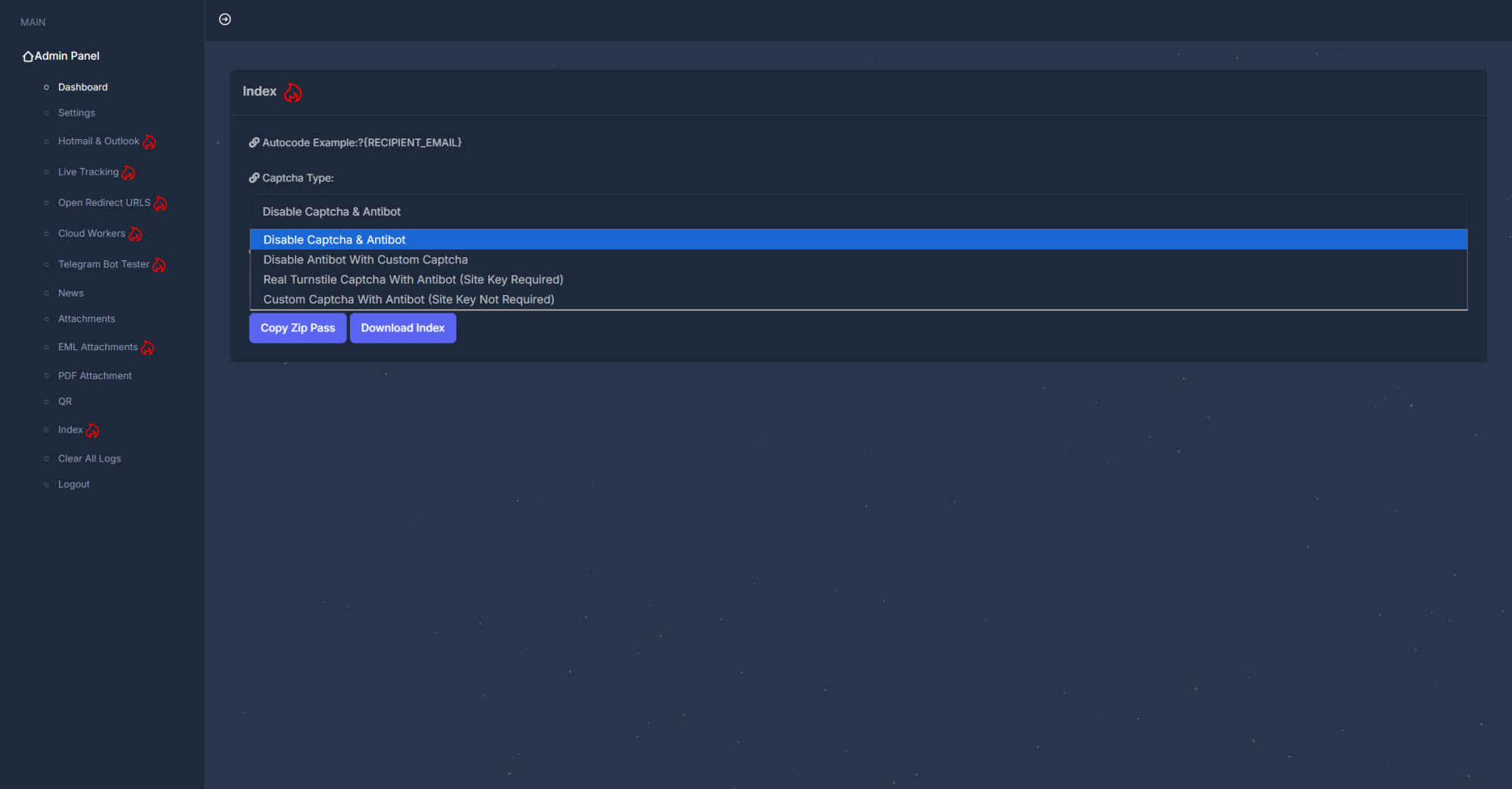
To protect the infrastructure behind Tycoon 2FA, cybercriminals used proprietary anti-bot solutions that detect popular search engines, antivirus engines, proxies, and VPNs, as well as IP addresses potentially associated with cybersecurity and content security providers.
Tycoon 2FA is undoubtedly among the best-in-class kits, targeting millions of consumers worldwide.
- Credential
harvesting for enterprise identity portals
The kit targets login
flows associated with Okta and Microsoft Active Directory Federation
Services (ADFS). In practice, this means it attempts to capture
usernames and passwords entered on spoofed single sign-on (SSO) pages
rather than collecting full accounts.
- Targeting
consumer email accounts
Built-in templates mimic Microsoft
consumer services (e.g., Hotmail and Outlook) to collect credentials
reused across corporate and personal environments.
- Open
redirect URL generation
The kit can generate phishing links that
exploit open redirect vulnerabilities to make URLs appear more
trustworthy or bypass basic domain filtering.
- CAPTCHA
imitation for social engineering
Fake verification elements
(e.g., imitation of Cloudflare Turnstile-style challenges) are used
purely to increase perceived legitimacy rather than provide real bot
filtering.
- Multiple
landing page templates
Operators can switch between several
visual templates that mimic common authentication portals.
-
Anti-bot and anti-debug protections
Includes filtering
mechanisms (blocking known headless bots or developer tools).
- Credential
exfiltration via Telegram
Captured data is automatically
forwarded via Telegram, a low-cost and effective exfiltration method.

